Privileged credentials are essential for managing enterprise IT ecosystems, yet they represent one of the most sensitive security assets. These credentials enable elevated access to servers, applications, databases, and automated services, making them a prime target for cyber threats. Many traditional security controls are not designed to handle the risks associated with such powerful access. CyberArk addresses this challenge through its Privileged Access Management framework, where Vaults and Safes act as core security pillars. For IT professionals, understanding how these components operate is crucial for protecting critical systems and maintaining operational trust. Advance your career in cybersecurity with our CyberArk Online Training, offering expert-led sessions that help you master privileged access management and secure digital identities from anywhere.
CyberArk Vault Concept
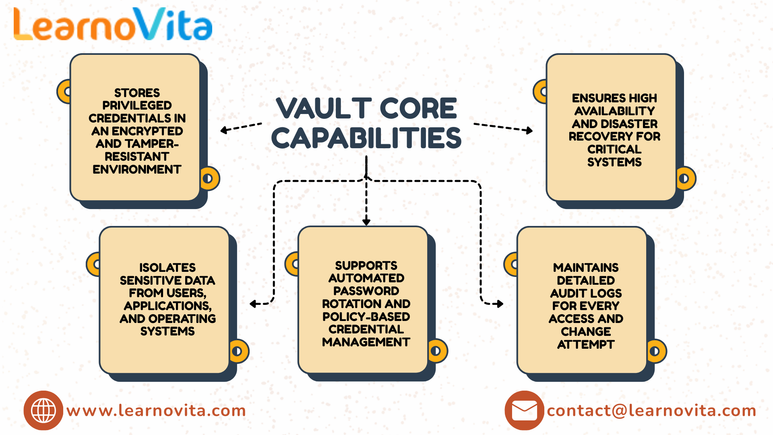
The CyberArk Digital Vault is a highly secure repository designed specifically to store and protect privileged credentials. Unlike standard password management tools, the Vault operates in a restricted and isolated environment that significantly reduces exposure to attacks. All credentials are encrypted using strong cryptographic mechanisms, ensuring they remain protected throughout their lifecycle. Passwords are never directly visible, even to administrators, which helps organizations minimize insider threats and prevent accidental credential leaks.
Vault Security Features
- Secures privileged credentials using enterprise-grade encryption
- Operates within a hardened and isolated infrastructure
- Enables automated password rotation based on defined policies
- Records all credential access and administrative activity
- Supports system stability through availability and recovery features
Purpose of CyberArk Safes
CyberArk Safes function as logical containers within the Vault, designed to organize privileged credentials in a structured and manageable way. Instead of maintaining all credentials in a single repository, Safes allow organizations to group access based on applications, environments, or operational ownership. This approach improves visibility, simplifies access control, and supports scalable credential governance across complex IT landscapes. Our Best Training & Placement Program ensures hands-on learning and career support, guiding you from skill-building to securing your dream job.
Permission Management in Safes
Safes provide granular control over how credentials are accessed and managed by users, applications, and automation tools. Permissions are configured to allow specific actions, such as secure credential retrieval or controlled password updates, without exposing the actual passwords. This access model ensures operational efficiency while enforcing least-privilege principles and reducing the risk of credential misuse.
Safe Design Guidelines
- Organize Safes based on application responsibility or environment scope
- Grant only the minimum permissions required for each role
- Apply consistent naming conventions for clarity and maintainability
- Enable automated credential rotation to reduce manual effort
- Review audit logs regularly to identify suspicious access patterns
Usage Across Modern IT
CyberArk Vaults and Safes are widely used across enterprise, cloud, and DevOps environments to protect privileged access. As organizations increasingly adopt cloud platforms and automation-driven workflows, the number of secrets such as service accounts, API keys, and access tokens continues to grow. Safes allow these credentials to be accessed securely at runtime without embedding them in code or configuration files, supporting modern IT practices while maintaining visibility and control.
Conclusion
CyberArk Vaults and Safes provide a strong and structured foundation for managing privileged access in modern IT environments. The Vault ensures robust credential protection through encryption and isolation, while Safes deliver organized storage and controlled access. Together, they help IT teams enhance security posture, support compliance requirements, and reduce exposure to credential-based threats. A clear understanding of these components is essential for professionals responsible for safeguarding sensitive systems and privileged access.