As cyber threats continue to evolve and increase in sophistication, organizations must adopt proactive measures to safeguard their digital assets. Ethical hacking provides a legal and structured way to detect vulnerabilities before malicious actors can exploit them. By simulating real-world attacks, ethical hackers help businesses uncover weaknesses and implement effective security measures. Mastering ethical hacking involves understanding attack techniques, conducting vulnerability assessments, and deploying strong defenses to protect critical systems and sensitive information. Unlock cybersecurity skills with our Ethical Hacking Online Training, designed to teach real-world hacking techniques in a legal and structured way.
Understanding Ethical Hacking
Ethical hacking is the authorized practice of testing networks, systems, and applications to identify potential security gaps and assess risks. White-hat hackers operate within legal and ethical boundaries, offering actionable insights to improve security. Beyond technical expertise, ethical hackers need analytical thinking, problem-solving skills, and strict adherence to ethical standards. Organizations benefit from ethical hacking through improved security, regulatory compliance, and increased resilience against cyber threats.
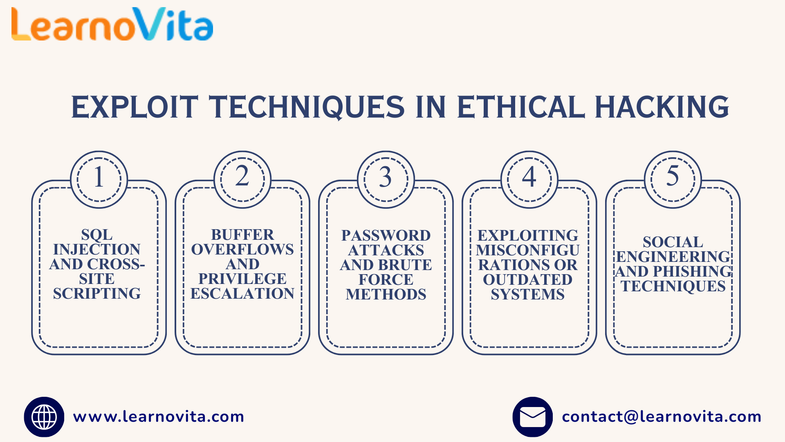
Common Exploit Methods
- SQL injection and cross-site scripting (XSS)
- Buffer overflow and privilege escalation
- Brute-force password attacks
- Exploiting outdated or misconfigured systems
- Social engineering and phishing attacks
Vulnerability Scanning
Vulnerability scanning is a key part of ethical hacking that identifies weaknesses in systems and networks. Automated tools detect unpatched software, misconfigurations, open ports, and exposed services. Ethical hackers analyze the results, prioritize vulnerabilities based on risk, and combine automated scans with manual testing. This comprehensive approach helps reduce the attack surface and strengthen overall cybersecurity posture.
Penetration Testing
Penetration testing goes beyond scanning by actively exploiting vulnerabilities in a controlled environment. Ethical hackers simulate real-world attacks on networks, applications, APIs, and other systems to assess potential impact. This process uncovers hidden weaknesses, evaluates the effectiveness of existing security measures, and provides actionable recommendations to enhance defenses. Our Best Training & Placement Program ensures hands-on learning and career support, guiding you from skill-building to securing your dream job.
Defense Strategies
- Maintain regular system updates and patch management
- Enforce secure configurations and access control policies
- Implement encryption and network segmentation
- Monitor networks and systems using intrusion detection tools
- Develop incident response plans and threat mitigation strategies
Skills and Tools for Ethical Hackers
Successful ethical hacking requires a combination of technical expertise, analytical thinking, and ethical judgment. Hackers need knowledge of networking, operating systems, programming, and scripting. Proficiency with scanning, exploitation, and reporting tools is essential, but knowing how to use them responsibly is equally important. Effective documentation and communication skills help translate findings into actionable security improvements. Continuous learning is crucial to keep up with evolving cyber threats and defense mechanisms.
Conclusion
Ethical hacking blends offensive techniques with defensive strategies to help organizations proactively manage cybersecurity risks. By understanding exploits, performing thorough vulnerability assessments, and implementing robust defenses, ethical hackers help minimize threats and strengthen security. Ethical hacking emphasizes resilience and protection rather than disruption. Organizations that adopt these practices foster proactive security cultures, safeguard critical assets, and maintain trust in an increasingly complex digital landscape.